You shouldn't post your email address to the web. Ever. In another article on harvesting emails (as a demo) we demonstrate how we stored nearly 5 million email Twitter addresses without effort. In the same way, you should never post your email address in a readable manner on your website because of the ease of which emails are harvested by spammers. This article will show you a quick way of obfuscating your email to make it just a little harder for some of the spammers to harvest your email.
Below is the very first snippet of shortcode we ever shared to one of our websites. Its purpose was simple: it meant that I could use [myemail] to render my email whenever is was required. I could add link text (usually a name so the function could be used by others) with the shortcode of [myemail name="marty"]. The result: marty. Simple... but careless.
It was a crappy solution. An email should never be posted in a readable form on a website because of the ease it's harvested by spam farmers. If you have a readable email on the web it's inevitable that you'll end up on any number of spammer distribution lists. It's the last function on this page that seeks to mitigate the risks by encoding your email - readable by a web browser, but less likely to be picked up by spammers.
The Spam Honeypot
It's impossible to catch all spam... but there was a phase I went through when I was determined to identify those that were sending me unsolicited email. I had a catch-all email address set up, and I included a hidden email on every page that would identify those that harvested the email by IP address. I used the following code in a hidden div on every page. It uses the beliefmedia_ip() function as provided on this page.
The shortcode of [iphoneypot] returns 3.143.228.88@test.com (3.143.228.88 being your IP address).
It was kind of a pointless exercise because I'd get thousands of emails that were harvested from hundreds of IP addresses... and I was always far too lazy to do anything about it.
At the time of originally writing this article (February, 2016) I experienced an influx of emails scraped from a few of my aviation websites by a company that identified as myAviationHUB... and it bothered me more than it normally did. The screenshot shows some of the emails that were sent within a short period - carrying titles such as "Aviation Goods & Services", "Aircraft for Sale", and "myAviationHUB" (among others). Each author on four of our aviation websites has been subscribed to at least a few of their lists without permission.
My action was limited: I reported MyAviationHub to list-manage.com and other authorities, and I listed their IP address as spam in a few global databases. I was particularly disappointed with this group simply because I expected more from aviation professionals.
However, the experience did make me dig a little deeper into rudimentary ways of obfuscating emails.
Obfuscate Your Email Addresses
While not ideal, we're now using a function that'll obfuscate any email address using a modified version of our former function.
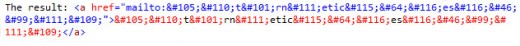
An obfuscated email for a test user on this site can be displayed with the shortcode of: [myemail username="BMTestUser"]MyTextInHere[/myemail]. The result: MyTextInHere. While the email is visible on the browser, it looks like this in the HTML source code:
If you would like to display link text without the opening and closing tags (handy when it's default text that renders all the time), use [myemail username="BMTestUser" text="email"]. The result: email. If no text is provided, we'll render your obfuscated email as the link label. Using a link label that isn't your email may offer another layer of protection against those that scrape rendered content rather than the HTML source.
While we use the login as an identifier, you may, of course, just use an email address as follows: [myemail username="test@test.com"]
The WordPress Shortcode
Copy and paste the WordPress function into your theme's functions.php file or, if you sensibly have one installed, your custom functions plugin.
If you require shortcode to work in a sidebar widget, you'll have to enable the functionality with a filter. If you're using our custom functions plugin, you'll have that feature enabled by default.
Shortcode Attributes
Following shortcode attributes are available.
username
username is the login name of the person whose email will be displayed. We use WordPress' get_user_by()  function to return an object with the user email. Alternatively, you may use any email address (validated by way of WP's funky is_email()
function to return an object with the user email. Alternatively, you may use any email address (validated by way of WP's funky is_email()  function).
function).text
text is the link text that will be displayed if you don't want to display your email as a link label. The text can be used as a shortcode attribute or it can be wrapped inside of your shortcode tags.hexencoding
hexencoding should normally be left as 'hexencoding' => 0 since it provides more predictable results. The WordPress antispambot  function documents a value of 0 for decimal encoding and 1 for hex encoding. However, a third undocumented and unsuitable option is 2 - providing a deeper obfuscation (see the naked PHP function below).
function documents a value of 0 for decimal encoding and 1 for hex encoding. However, a third undocumented and unsuitable option is 2 - providing a deeper obfuscation (see the naked PHP function below).The WordPress Function Used Outside of WordPress
The WordPress antispambot() function - located in 
wp-includes/formatting.php - can easily be used in any PHP application. The code is as follows:
Considerations
- The antispambot
 function is one of those unknown functions that doesn't attract a great deal of mainstream attention and, for that reason, many have written inferior code to accomplish what the existing function already does. Rewriting existing WordPress functions out of "core" ignorance is something I'm guilty of myself (numerous times) so that remark isn't intended as criticism.
function is one of those unknown functions that doesn't attract a great deal of mainstream attention and, for that reason, many have written inferior code to accomplish what the existing function already does. Rewriting existing WordPress functions out of "core" ignorance is something I'm guilty of myself (numerous times) so that remark isn't intended as criticism.
- Showing your email address publicly is never a good idea. Instead, just link to a contact page.
- We'll look at other way of mitigating spam in the future.
Download
Title: Obfuscate Email Addresses in WordPress (WP Plugin)
Description: Obfuscate Email Addresses with PHP or WordPress shortcode.
Download • Version 0.2, 1.5K, zip, Category: WordPress Plugins (General)
WordPress Shortcodes, (614.0B) PHP Code & Snippets, (815.0B)